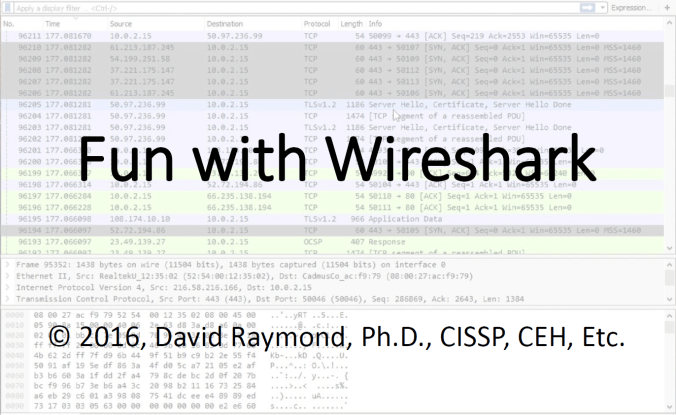
Another great meeting with a lot new faces and a lot of familiar ones. Big “Thanks!” to David Raymond (@dnomyard) for presenting and ECPI for hosting. David was kind enough to provide us a copy of the slides, you can grab them here:
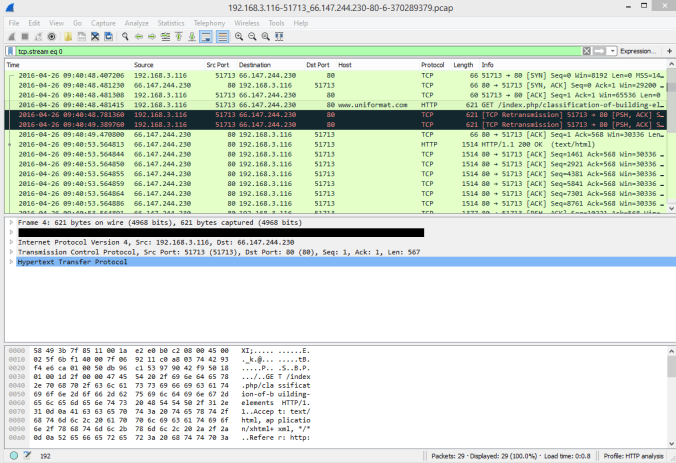
If you want some more practice with pcaps and malware definitely check out: http://www.malware-traffic-analysis.net/ Just be careful if you export HTTP Objects out of those as they do contain actual malware. Don’t infect yourself! 🙂
out of those as they do contain actual malware. Don’t infect yourself! 🙂
Brad (@malware_traffic), who runs that site, does an outstanding job posting tutorials as well as breakdowns of current samples and traffic patterns. He joined Unit 42, Palo Alto’s Threat Research group,which does some excellent in depth write-ups on malware. This write-up on Locky ransomware and Nuclear EK is a good example: http://researchcenter.paloaltonetworks.com/2016/03/locky-ransomware-installed-through-nuclear-ek/
 David Raymond presenting
David Raymond presenting
 David, Michael and Rob
David, Michael and Rob
 Just talkin’ shop
Just talkin’ shop
Also, don’t forget the RBTC Vulnerability Management forum is coming up as well as RVASec. If you know of other “local” security events please email roanokeinfosec@gmail.com and we will get them posted to the site.
Last but not least, if there is a topic that you would like to request for a presentation please let us know. We will do our best to line up a speaker. Or if you can speak on a topic please let us know and we’ll get you in the line up!