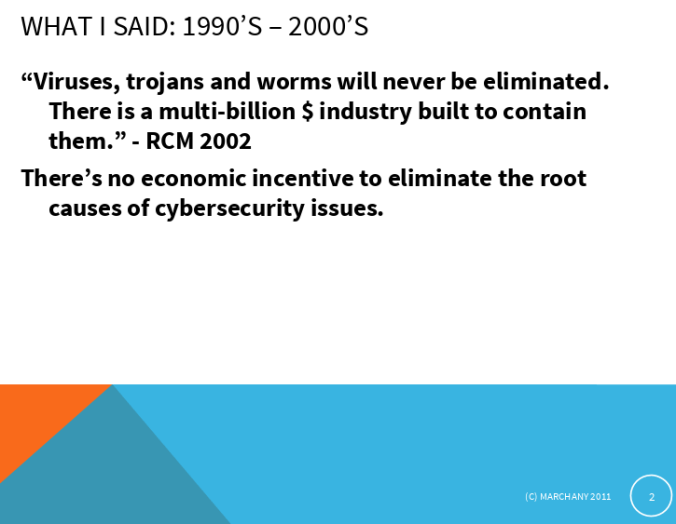
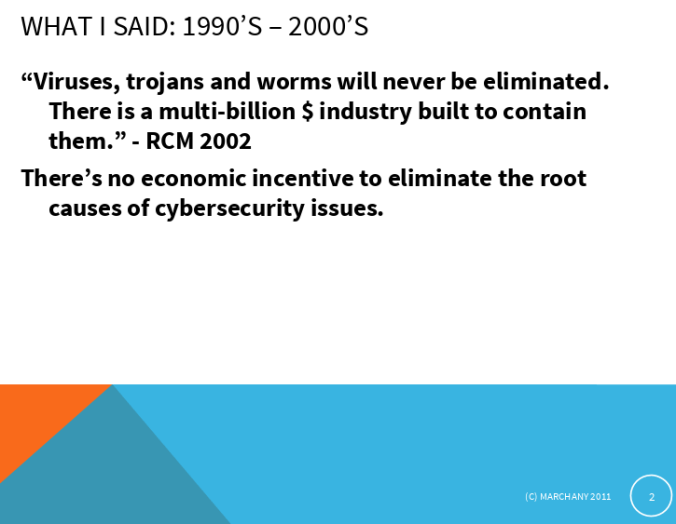
At our Dec. meeting our guest speaker was Randy Marchany (bio below). @randymarchany is the University Information Security Officer for Virginia Tech. He is also the director of the VA Tech IT Security Lab, a component of the university’s Information Technology Security Office. Randy did a great presentation about Continuous Monitoring and how they are implementing it at Virginia Tech. He also talked about how security is changing with “borderless” computing. They have to blend corporate security with ISP model security. He also talked about as much as things change, some seem to stay the same. One of my favorite slides from the presentation was a quote Randy said back in 2002, that still holds very true today:
Here is the “Continuous Security Monitoring: A Big Data Challenge” presentation:

Here is the “What is Old is New Again” presentation:

Randy’s bio:
Randy Marchany is the University Information Security Officer for Virginia Tech. He is also the director of the VA Tech IT Security Lab, a component of the university’s Information Technology Security Office.
He is the author of VA Tech’s Acceptable Use Statement and a co-author of the original FBI/SANS Institute’s “Top 10/20 Internet Security Vulnerabilities” document. He is the co-author of the SANS Institute’s “Responding to Distributed Denial of Service Attacks” document that was prepared at the request of the White House in response to the DDOS attacks of 2000. He was part of the SANS Institute’s Secure Code project that developed a set of exams to test programmers’ knowledge of secure coding techniques. He has been a member of the SANS Institute’s faculty since 1992.
He is a co-author of the EDUCAUSE “Computer and Network Security in Higher Education” booklet. He is a member of the EDUCAUSE security task force focusing on risk assessment and security metrics. He was a coauthor of the original Center for Internet Security’s series of Security Benchmark documents for Solaris, AIX and Windows2000.
He is one of the original members of the US Cyber Challenge (USCC) Project. The USCC mission is to significantly reduce the shortage in the cyber workforce by serving as the premier program to identify, attract, recruit and place the next generation of cybersecurity professionals. He designed the curriculum for the USCC summer camps.
He is one of the founders of the Virginia Alliance for Secure Computing and Networking (www.vascan.org), a consortium of security practitioners and researchers from VA Tech, U of Virginia, James Madison Univ., George Mason Univ.
He has been a frequent speaker at national and international conferences such as Educause, SANS, IIA, ISACA, ACUA, International CISO symposium, IEEE, NIST, NY State OIT Security conference, FBI-Infraguard chapters, US Forest & Wildlife Service, Computer Security Conference, Air Force Material Command. He’s been the subject of articles in the Chronicle of Higher Education on security issues at university campuses.
He was a recipient of the SANS Institute’s Security Technology Leadership Award for 2000. He was a recipient of the VA Governor’s Technology Silver Award in 2003. He was part of the team that won the EDUCAUSE Excellence in Information Technology Solutions Award in 2005. He is a co-holder of two cybersecurity patents.
He is acknowledged as one of the North American masters of the hammer dulcimer. He is the author of the original theme song of National Public Radio’s nationally syndicated radio program, “World Cafe”. His band, “No Strings Attached” was nominated for or won “Indie” awards (independent record label’s version of the Grammy) for Best Album (String Music) category in 1984, 1985, 1986, 1988, 1990.