Meeting info: May 12th, @6pm, at ECPI (directions below).
This meeting is a can’t miss opportunity for a hands on deep dive with Wireshark. David Raymond (@dnomyard, bio below) who has previously spoken at Black Hat USA, RSA and Scmoocon will be presenting.
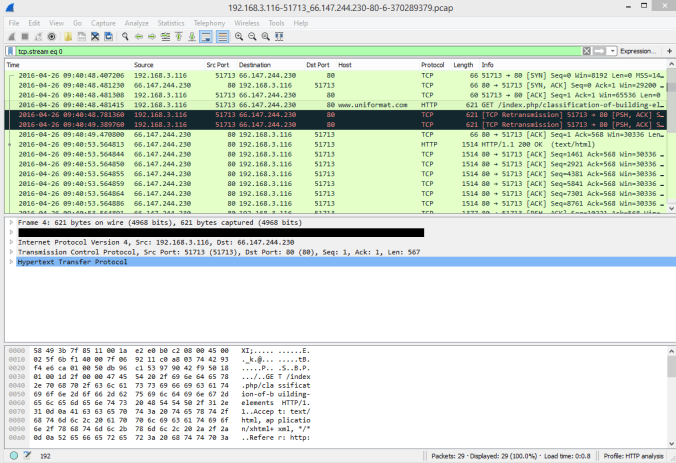
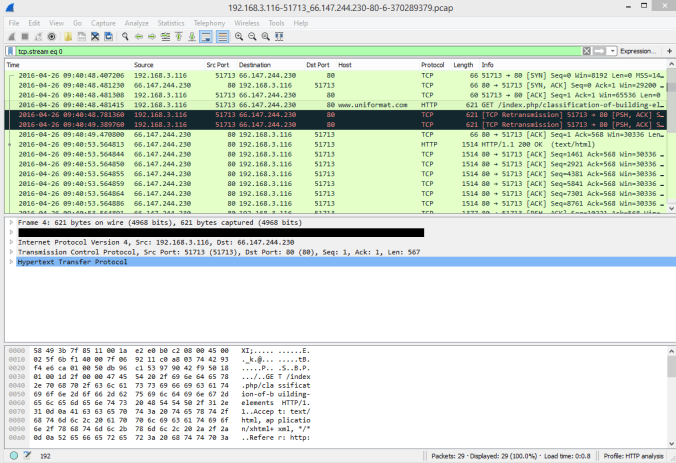
Wireshark is a great tool for quick-and-dirty network traffic analysis and it is widely used for network troubleshooting and incident response. In this hands-on discussion, we will review the basics of Wireshark and discuss capture filters, display filters, and basic protocol analysis. We’ll then go beyond the basics to talk about more advanced features of Wireshark and touch on some of the command-line utilities that come with it, such as tshark, editcap, mergecap, and randcap.
To get the most from the discussion, attendees should bring a laptop with the latest version of Wireshark installed.
ECPI (5234 Airport Rd NW #200, Roanoke, VA 24012 or Google Maps) will be hosting the meeting and there will be some lab machines available for use by those without a laptop available.
David Raymond currently serves as Deputy Director in the Virginia Tech IT Security Office and Lab. In this position he helps oversee the security of the VT network, advises graduate students and undergrads doing cybersecurity research, and teaches courses in computer networking and security in the Department of Electrical and Computer Engineering. David holds a Ph.D. in Computer Engineering from Virginia Tech, a Masters in Computer Science from Duke University, and a Bachelors in CS from West Point. He has published over 25 journal and conference publications on a variety of topics and has spoken at numerous industry and academic conferences to include Black Hat USA, RSA, Shmoocon, and the NATO Conference on Cyber Conflict.