RISE is excited to announce our July meeting – a cook-out hosted by ABS Technology! We are asking for RSVPs for this event so please read below if you plan to attend.
Our next meeting on Thursday, July 12, will be held at ABS Technology’s office in downtown Roanoke. Join us at 5:30pm for some great food in the view of Roanoke’s Downtown Historic District. Don’t worry about that summer heat as there will be plenty of ISE…Cisco Identity Services Engine. Speaker Lee Berdick will introduce ISE and discuss how it provides secure network access to users and devices.
Date: Thursday, July 12, 5:30pm
Address: ABS Technology, 109 Norfolk Ave, 2nd Floor, Roanoke, VA
RSVP REQUESTED! Please respond to roanokeinfosec@gmail.com if you will be there so we may estimate attendance. Free parking information will be provided to those who RSVP in advance. We don’t normally ask for this and appreciate your understanding so we can help our hosts plan for this special event.
Topic: Cisco ISE
Cisco ISE allows you to provide highly secure network access to users and devices. It helps you gain visibility into what is happening in your network, such as who is connected, which applications are installed and running, and much more. It also shares vital contextual data, such as user and device identities, threats, and vulnerabilities with integrated solutions from Cisco technology partners, so you can identify, contain, and remediate threats faster.
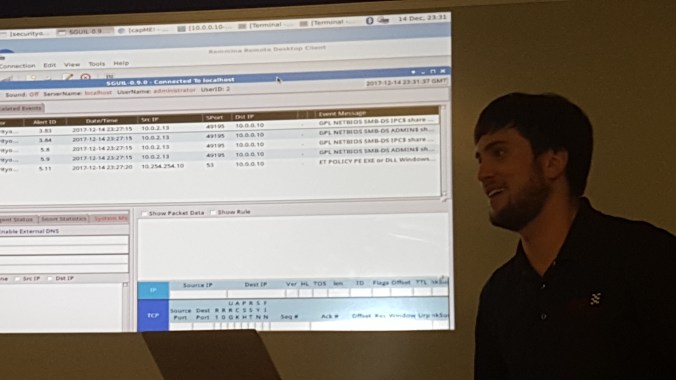
Speaker Bio: Lee Berdick
Lee joined ABS Technology in 2017 as a Senior Solutions Consultant. He graduated from Florida State University with a degree in Information Studies and a Graduate Certificate in Library Information Science.
Lee has been passionate about the IT field since he was 17 years old. It has been a central focus and interest in his life that led him to his career path. He holds several certifications including Certified Cisco Network Associate, Certified Cisco Design Associate, ITILv3, Palo Alto Networks Accredited Configuration Engineer, Splunk – SE I.
Outside of IT, Lee produces and DJ’s electronic dance music and has an extensive vinyl record collection with over 3,500 pieces.

(source: dilbert.com)