As the spring rains settle over the Roanoke Valley, there is something about the atmosphere of a rainy April evening that pairs perfectly with a deep-dive technical session behind the glow of a screen. We’re heading back into the lab this month to take shelter from the showers and focus on the latest in kernel security.
Here is a look at what’s happening this month:
- April 9 @ 5:45 PM: Pre-meeting RISE Financial Update (Non-Profit status).
- April 9 @ 6:00 PM: Main Meeting: Tyler “dru1d” Booth presents “Make No Mistake: Kernel Hacking with AI.”
- June 5: BSides Roanoke 2026 – Tickets are moving fast.
- Final Call: The BSides CFP is reaching its deadline—submit your proposals now.
Special Announcement: RISE Financials
Time: 5:45 PM (15 minutes before the main event)
Now that RISE is officially a non-profit, we want to be transparent with the community that keeps us running. We will be presenting the RISE financials briefly before our guest speaker begins.
Arrive early to dodge the showers and see how we’re bootstrapping the future of RISE.
RISE Meeting: Make No Mistake: Kernel Hacking with AI
Time: 6:00 PM
This month, we are excited to welcome Tyler “dru1d” Booth, who will show us how modern AI can be used to navigate the complex world of kernel driver reverse engineering.
About the Talk
Kernel driver reverse engineering has always been a slow, painful grind. Weeks of decompilation, IOCTL tracing, and hunting for known exploit primitives. But what if you could compress months of work into days with AI models doing the heavy lifting?
Tyler will walk through building an AI-assisted kernel exploitation workflow, from purpose-built agent pipelines to the pragmatic reality of manually steering Claude through driver triage and weaponization.
In this session, we’ll cover:
- HEXXUS: A platform of specialized AI agents (triager, exploit dev, crash handler, orchestrator) backed by custom MCP servers for WinDbg, Hyper-V, and Binary Ninja. What happens when you try to fully automate driver exploitation, and how much it can run up your API bill.
- CASE STUDY: INFOHAZARD BOF: Four days from VirusTotal target identification to a fully weaponized Beacon Object File: kernel virtual memory read/write, token manipulation, credential dumping, process integrity modification, and kernel callback enumeration/removal. The kind of project that used to take a month or two.
- What We Learned: Where AI actually helped, where it hallucinated, and why you still need to double-check your agents’ work.
Meeting Details:
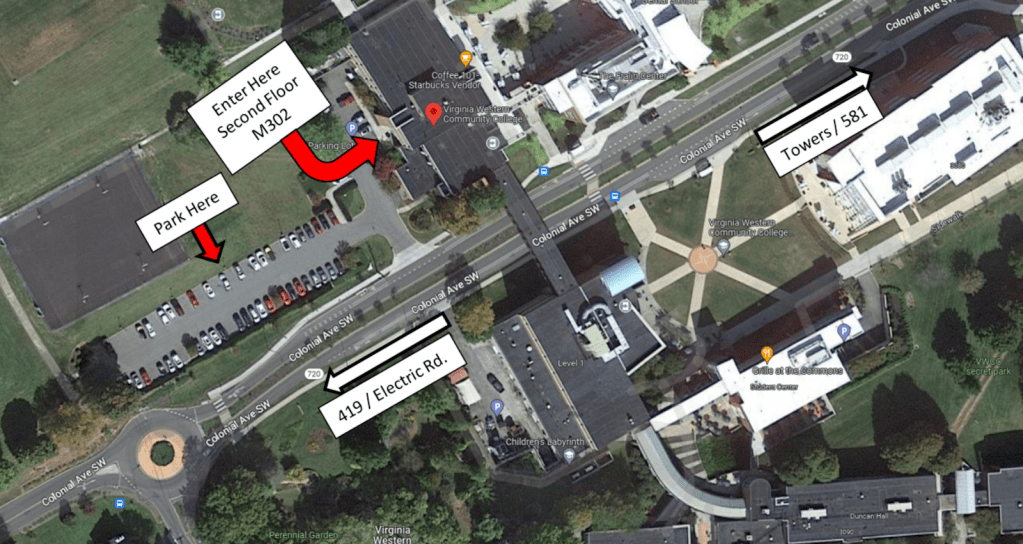
Whether you are a seasoned professional or just getting started in the field, we invite you to join us at Virginia Western Community College in the Hall Family Business/Science Building. We’ll be meeting on the third floor in the CyberSecurity lab, Room M302.
Meeting Info:
- Location: VWCC Business/Science Building, Room M302
- Date: April 9th, 2025
- Financials Start: 5:45 PM
- Main Presentation: 6:00 PM
- View Map
Tickets: BSides Roanoke 2026
Don’t wait until the last minute. General admission tickets for BSides Roanoke 2026 (June 5th) are available. Join us for a full day of technical talks and workshops right here in Roanoke.
Purchase Tickets: https://www.zeffy.com/en-US/ticketing/bsides-roanoke–2026
Final Call: BSides Roanoke 2026 CFP
The window is closing fast. If you have a breakthrough, a unique case study, or a tool you’ve been building, we want to see it on the big stage this June. If you submit after April 5th, it might be too late.
Submit here: https://forms.gle/XXXgp2fysP91v4oR9
We look forward to seeing you all on April 9th for RISE and June 5th for BSides Roanoke!